Which SQL function is used to extract the day of the week from a date?
c) DAYNAME() is used to extract the day of the week from a date in SQL.
It returns a string representing the day of the week (e.g. "Monday", "Tuesday", etc.) for the given date.
 Additional InformationIn SQL, DATE() is a function that can be used to extract the date part of a DATE or DATETIME value.
Additional InformationIn SQL, DATE() is a function that can be used to extract the date part of a DATE or DATETIME value.
YEAR() function can be used to extract the year part of a DATE or DATETIME value.
MONTH() function can be used to extract the month part of a DATE or DATETIME value.
Match the following lists:
|
(a) |
Bus Topology |
(i) |
Combination of star and Bus Topology |
|
(b) |
Ring Topology |
(ii) |
Uses a single cable that connects all the nodes |
|
(c) |
Mesh |
(iii) |
Uses tokens to pass the information from one computer to another computer |
|
(d) |
Tree |
(iv) |
Every node is directly connected |
The Correct answer is (a) - (ii), (b) - (iii), (c) - (iv), (d) - (i).
 Key Points
Key Points
- Bus Topology: Uses a single cable that connects all the nodes.
- Ring Topology: Uses tokens to pass the information from one computer to another computer.
- Mesh Topology: Every node is directly connected.
- Tree Topology: Combination of star and bus topology.
 Additional Information
Additional Information
- Bus Topology
- In a bus topology, all devices share a single communication line or cable.
- It is cost-effective for small networks.
- However, if the main cable fails, the entire network goes down.
- Ring Topology
- In a ring topology, each device has exactly two neighbors for communication purposes.
- A token-passing protocol is used to prevent collisions.
- Failure in any single device can disrupt the entire network.
- Mesh Topology
- In a mesh topology, each node is connected to every other node.
- Provides high redundancy and reliability.
- It is expensive and complex to install and manage.
- Tree Topology
- A tree topology is a combination of star and bus topologies.
- It has a hierarchical flow of data.
- Useful for large networks and can be easily expanded
Concept:
The ALTER TABLE statement is used to add, delete, or modify columns in an existing table.
The ALTER TABLE statement is also used to add and drop various constraints on an existing table.
ADD Column
To add a column in a table, use the following syntax:
ALTER TABLE table_name ADD column_name datatype;
DROP COLUMN
To delete a column in a table, use the following syntax (notice that some database systems don't allow deleting a column):
ALTER TABLE table_name DROP COLUMN column_name;
The correct answer is option 2.
Concept:
Relational algebra is a procedural query language, which takes instances of relations as input and yields instances of relations as output.
It uses operators to perform queries. An operator can be either unary or binary. They accept relations as their input and yield relations as their output. Relational algebra is performed recursively on relation and intermediate results are also considered relations.
The fundamental operations of relational algebra are as follows:
- Select (σ)
- Project (∏)
- Union (∪)
- Set different (−)
- Cartesian product (Χ)
- Rename (ρ)
Hence the correct answer is procedural.
Consider the table given below:
Table : STUDENT
| ADMNO | NAME | CLASS | SCORE |
| A001 | Amit | 12A | 90 |
| A002 | Amit | 12B | 91 |
| A003 | Bhavana | 12A | 90 |
| A004 | Yamini | 12A | 89 |
| A005 | Ashok | 12B | 95 |
Using the STUDENT table, you want to execute a SQL query to find all records where the NAME starts with the letter "A". Which of the following SQL commands correctly accomplishes this?
The correct answer is SELECT * FROM STUDENT WHERE NAME LIKE 'A%';
 Key Points
Key Points
- The LIKE operator is used in SQL to search for a specified pattern in a column. In the correct command (option 1), the pattern 'A%' signifies any string that starts with "A".
- The percent sign (%) represents zero or more characters, making 'A%' a match for any names beginning with "A".
- This option accurately fetches records for "Amit" and "Ashok", fitting the criteria.
 Additional Information
Additional Information
- Option 2 uses the equals sign, which is incorrect for pattern matching.
- Option 3 searches for names ending with "A", which does not match the question's requirement.
- Option 4 expects names to consist of only two characters, the first being "A" and the second being any character, which doesn't correctly represent the requirement and would not match any names in the given table accurately.
Consider the table given below:
Table : STUDENT
| ADMNO | NAME | CLASS | SCORE |
| A001 | Amit | 12A | 90 |
| A002 | Amit | 12B | 91 |
| A003 | Bhavana | 12A | 90 |
| A004 | Yamini | 12A | 89 |
| A005 | Ashok | 12B | 95 |
Using the STUDENT table, you want to select all records where the CLASS is either '12A' or '12B'. Which of the following SQL commands correctly achieves this?
A. SELECT * FROM STUDENT WHERE CLASS = '12A' OR CLASS = '12B';
B. SELECT * FROM STUDENT WHERE CLASS IN ('12A', '12C');
C. SELECT * FROM STUDENT WHERE CLASS IN ('12A', '12B');
D. SELECT * FROM STUDENT WHERE CLASS = '12A' AND '12B';
The correct answer is Only A and C
 Key Points
Key Points
- The IN operator allows you to specify multiple values in a WHERE clause.
- The correct use of the IN operator (statement C) concisely checks for records where the CLASS column is either '12A' or '12B'.
- This command is more efficient and readable compared to using multiple OR conditions for the same criteria.
- Statement A achieves a similar result but uses a longer syntax because it separates the conditions with OR. So it is also correct.
The correct answer is Update.
 Key Points
Key Points
- The UPDATE command in SQL is used to modify existing records in a table.
- It allows you to change one or more columns for a specified row or rows.
- The syntax for the UPDATE statement is:
UPDATE table_name SET column1 = value1, column2 = value2, ... WHERE condition; - Without a WHERE clause, all rows in the table will be updated.
 Additional Information
Additional Information
- INSERT: This command is used to add new rows to a table. It cannot be used to modify existing data. Syntax:
INSERT INTO table_name (column1, column2, ...) VALUES (value1, value2, ...); - BROWSE: This is not a standard SQL command. It might be used in some database management systems for navigating through the data, but it is not used to modify data.
- APPEND: This is also not a standard SQL command. In some contexts, it might mean adding new data to the end of a table, but the standard SQL command for this operation is INSERT.
The correct answer is Relation database management system.
 Key Points
Key Points
- Relational Data Base:
- A relational database is a collection of data items with pre-defined relationships between them.
- These items are organized as a set of tables with columns and rows.
- Tables are used to hold information about the objects to be represented in the database.
- Each column in a table holds a certain kind of data and a field stores the actual value of an attribute.
- The rows in the table represent a collection of related values of one object or entity.
- Each row in a table could be marked with a unique identifier called a primary key, and rows among multiple tables can be made related using foreign keys.
- This data can be accessed in many different ways without reorganizing the database tables themselves.
- Examples: Popular examples of standard relational databases include Microsoft Access, Microsoft SQL Server, Oracle Database, MySQL, and IBM DB2. Cloud relational databases include Amazon Relational Database Service (RDS), Google Cloud SQL, IBM DB2 on Cloud, SQL Azure, and Oracle Cloud.
 Additional Information
Additional Information
- Hierarchical database management system:
- This refers to a type of database management system that organizes data in a tree-like structure with a single root, to which all the other data is linked.
- Object-oriented management system:
- Object-oriented database management systems (OODBMS) store data in the form of objects, which are instances of classes.
The correct answer is drop.
 Key Points
Key Points
- The DROP statement in SQL is used to delete a table or a database. When you drop a table, it deletes the table structure along with all the data, indexes, triggers, constraints, and relationships.
 Additional Information
Additional Information
- REVOKE: This statement is used to remove permissions granted to a user or role in SQL. It does not affect the table structure or data.
- DELETE: This statement is used to delete records from a table. However, it does not remove the table structure or relationships.
- TRUNCATE: This statement is used to delete all rows from a table, but it does not delete the table structure or relationships.
The correct answer is REVOKE
 Key Points
Key Points
- A database system provides a data-definition language (DDL) to specify the database schema
Example of DDL commands: CREATE, DROP, RENAME, TRUNCATE etc.
 Additional Information
Additional Information
- A data-manipulation language (DML) is a language that enables users to access or manipulate data as organized by the appropriate model
Example of DML commands: INSERT, DELETE, UPDATE etc.
- A data control language (DCL) is used to control access (Authorization) to data stored in a database
Example of DCL commands: GRANT and REVOKE
The correct answer is Router.
 Key Points
Key Points
- A router is a networking device that forwards data packets between computer networks.
- Routers perform the traffic directing functions on the Internet. Data sent through the internet, such as a web page or email, is in the form of data packets.
- A data packet is typically forwarded from one router to another through the networks that constitute the internetwork until it reaches its destination node.
- A router is connected to two or more data lines from different networks. When a data packet comes in on one of the lines, the router reads the network address information in the packet to determine its ultimate destination.
- Then, using information in its routing table or routing policy, it directs the packet to the next network on its journey.
 Additional Information
Additional Information
- Routers can connect different network architectures, such as Ethernet and Wi-Fi.
- They typically include a built-in firewall to protect against unauthorized access and cyber threats.
- Modern routers often come with additional features like Quality of Service (QoS) settings to prioritize certain types of traffic.
- Some routers also include built-in VPN (Virtual Private Network) capabilities to enhance security and privacy.
Assertion (A): The HAVING clause is used to filter rows after the aggregation process.
Reason (R): The WHERE clause cannot filter aggregated results, hence the HAVING clause is used after GROUP BY to apply conditions on aggregated data.
Choose the correct option:
The correct answer is Both A and R are true, and R is the correct explanation of A.
 Key Points
Key Points
- Assertion (A): The HAVING clause is used to filter rows after the aggregation process.
- This assertion is true. The HAVING clause in SQL is utilized to filter groups created by GROUP BY based on some condition. This happens after the aggregation process so you can apply conditions on aggregated data like the sum or count of rows in each group.
- Reason (R): The WHERE clause cannot filter aggregated results, hence the HAVING clause is used after GROUP BY to apply conditions on aggregated data.
- This reason is correct and offers a valid explanation as to why the HAVING clause exists and is used. The WHERE clause cannot be applied directly to aggregate functions like SUM, COUNT, etc. Therefore, the HAVING clause is specifically designed for such a scenario, acting as a WHERE clause for aggregated groups.
The correct answer is IP address.
 Key Points
Key Points
- An IP address (Internet Protocol address) is a unique string of numbers separated by periods (IPv4) or colons (IPv6) that identifies each computer using the Internet Protocol to communicate over a network.
- Every device connected to the internet has a unique IP address, which allows it to be identified and located.
- IP addresses are used by network devices to send and receive data packets across the internet.
- There are two types of IP addresses: IPv4 (e.g., 192.168.1.1) and IPv6 (e.g., 2001:0db8:85a3:0000:0000:8a2e:0370:7334).
- IP addresses can be static (permanently assigned) or dynamic (temporarily assigned by a DHCP server).
 Additional Information
Additional Information
- IP addresses are managed and allocated by the Internet Assigned Numbers Authority (IANA) and regional internet registries (RIRs).
- Network administrators and Internet Service Providers (ISPs) are responsible for assigning IP addresses to devices within their networks.
- IP addresses play a crucial role in routing data packets to their correct destinations on the internet.
- IP addresses can reveal general information about the location of a device, such as the country or city in which it is located.
- Network security and privacy measures often involve managing and protecting IP addresses to prevent unauthorized access and cyber threats.
 Key Points
Key Points
- A Bridge is used to connect two local area networks (LANs) that use the same protocol.
- It operates at the data link layer (Layer 2) of the OSI model.
- Bridges are used to segment a network, reduce collisions, and manage traffic efficiently.
- They can filter traffic and reduce the amount of traffic on a LAN by dividing it into segments.
- Unlike hubs and switches, bridges can be used to connect different types of networks, such as Ethernet and Wi-Fi networks, as long as they use the same protocol.
 Additional Information
Additional Information
- Hub: A hub is a basic networking device that connects multiple computers in a LAN but does not manage traffic or reduce collisions.
- Modem: A modem is a device that modulates and demodulates signals for communication over telephone lines or cable systems.
- Switch: A switch is a more advanced device than a hub that connects devices in a LAN and uses MAC addresses to forward data only to the intended recipient.
- Router: Although not listed as an option, a router is used to connect different networks, such as a LAN to a WAN (Wide Area Network).
- Bridges are essential for expanding networks and improving performance by dividing large networks into smaller, more manageable segments.
Which is/are the correct statement given about a relation?
I. In relational algebra, selection may return duplicate tuples.
II. In relational algebra, projection will never return duplicate column.In relational algebra, selection and projection will never return duplicate entries.
|
Symbol |
Name |
Example |
|
σ |
selection |
σA = 500(R) → Return rows whose A attribute is equal to 500 and no duplicates are allowed |
|
∏ |
projection |
∏B(R) → Output the column B and no duplicate are allowed |
| List I | List II | ||
| (a) | DCL | (i) | LOCK TABLE |
| (b) | DML | (ii) | COMMIT |
| (c) | TCL | (iii) | Natural Difference |
| (d) | Binary operation | (iv) | REVOKE |
Correct Answer: Option 3
Explanation:
- DCL stands for Data Control Language. DCL includes commands such as GRANT and REVOKE which mainly deal with the rights, permissions, and other controls of the database system. The REVOKE command withdraws the permissions from a user on a database object or schema. Since it modifies the users who can access a schema, REVOKE is a DCL command.
- DML stands for Data Manipulation Language. This includes commands that modify the data contained in the database. It can enter new data, delete existing data and change the data. A LOCK TABLE command is implicitly applied when an INSERT, UPDATE, DELETE, MERGE and SELECT command is being executed. Therefore, LOCK TABLE is a DML command.
- TCL stands for Transaction Control Language. They are used to maintain the integrity of the database tables and are committed at the end of any DML operation. Thus, COMMIT is a TCL command.
- A binary operation is a set operation that is performed between two database tables. The natural difference finds the set difference between two database schemas and so it is a binary operation.
The correct option is (4)
The virus cannot be detected
Concept:-
Viruses can be detected by having an antivirus program.
 Key Points
Key Points
- A computer virus is a little piece of software that interferes with computer operation and spreads from one machine to another.
- A computer virus may corrupt or remove data on a computer, spread to other computers via email, or even delete all data on the hard drive.
- In emails and instant communications, attachments are routinely used to propagate computer infections.
- A harmful software, script, macro, or piece of code known as a computer virus is made to harm your computer, steal your personal information, alter data, send emails, show messages, or do a combination of these things.
- The computer virus has a propensity to quickly create copies of itself, spread to every folder, and corrupt the data on your computer system.
 Additional Information
Additional Information
- A lawful software can contain code that is designed to "explode" when specific criteria are met. This code is known as the "Logic Bom."
The correct answer is SQL.
 Key Points
Key Points
- SQL (Structured Query Language) is a standardized programming language specifically designed for managing and manipulating relational databases.
- It has become the defacto standard for interfacing application programs with relational database systems because of its ubiquity and ease of use.
- SQL allows users to query, update, insert, and delete data in a database, making it an essential tool for database management.
- Due to its standardization by organizations like ANSI and ISO, SQL is widely adopted across various database systems such as MySQL, PostgreSQL, Oracle, and SQL Server.
 Additional Information
Additional Information
- Oracle: Oracle is a popular relational database management system (RDBMS) but it is not a language. It uses SQL as its query language.
- dBASE: dBASE is a database management system (DBMS) that was popular in the 1980s and early 1990s. It has its own programming language called dBASE, but it did not become a standard like SQL.
- 4GL (Fourth Generation Language): 4GL refers to a class of programming languages that are closer to human language than typical high-level programming languages. While useful, 4GLs are not standardized for relational databases like SQL.
Assertion (A): A query using the GROUP BY clause can also use the WHERE clause to filter rows before they are grouped.
Reason (R): The WHERE clause is processed before the GROUP BY clause in the SQL query execution order, allowing for pre-group filtering of rows.
Choose the correct option:
The correct answer is Both A and R are true, and R is the correct explanation of A.
 Key Points
Key Points
- Assertion (A): A query using the GROUP BY clause can also use the WHERE clause to filter rows before they are grouped.
- This assertion is true. The WHERE clause is used to filter rows based on a specified condition before those rows are grouped by the GROUP BY clause. This pre-grouping filter is a common practice to narrow down the dataset to the relevant rows before aggregation.
- Reason (R): The WHERE clause is processed before the GROUP BY clause in the SQL query execution order, allowing for pre-group filtering of rows.
- This reason is correct and serves as the proper explanation for why you can use a WHERE clause with GROUP BY. The order of operations in SQL ensures that rows are first filtered by the WHERE clause before any grouping occurs.
The correct answer is selection.
 Key Points
Key Points
- The selection sort algorithm divides the array into two parts: a sorted sublist of items which is built up from left to right at the front (left) of the array and a sublist of the remaining unsorted items that occupy the rest of the array.
- Initially, the sorted sublist is empty and the unsorted sublist is the entire input list.
- The selection sort algorithm proceeds by finding the smallest (or largest, depending on sorting order) element from the unsorted sublist, swapping it with the leftmost unsorted element (putting it in sorted order), and moving the sublist boundaries one element to the right.
 Additional Information
Additional Information
- Bubble sort is a simple sorting algorithm that repeatedly steps through the list, compares adjacent elements and swaps them if they are in the wrong order. The pass through the list is repeated until the list is sorted. It does not explicitly divide the array into sorted and unsorted sublists.
- Insertion sort works similarly to the way you might sort playing cards in your hands. It builds the final sorted array (or list) one item at a time, with the sorted section growing from left to right. However, it does not explicitly maintain separate sorted and unsorted sublists.
The Correct answer is star.
 Key Points
Key Points
- Star Topology:
- A star topology is designed with each node (file server, workstations, and peripherals) connected directly to a central network hub, switch, or concentrator.
- Data on a star network passes through the hub, switch, or concentrator before continuing to its destination.
- The hub, switch, or concentrator manages and controls all functions of the network.
- It also acts as a repeater for the data flow.
- This configuration is common with twisted pair cable; however, it can also be used with coaxial cable or fiber optic cable.
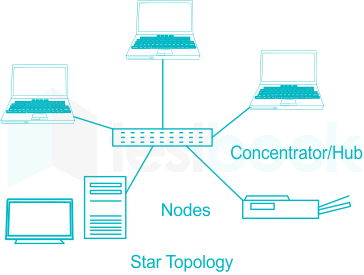
 Additional Information
Additional Information
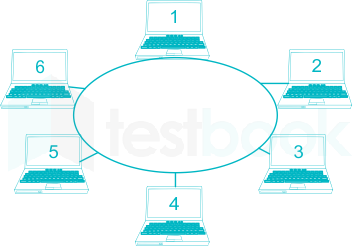
- Ring Topology;
- In ring topology each node connects to exactly two other nodes, forming a single continuous pathway for signals through each node - a ring.
- Data travels from node to node, with each node along the way handling every packet.
- Because a ring topology provides only one pathway between any two nodes, ring networks may be disrupted by the failure of a single link.
- A node failure or cable break might isolate every node attached to the ring.
- Bus topology:
- Linear bus topology is a type of network topology where each device connects one after the other in a sequential chain
- The bus topology is designed in such a way that all the stations are connected through a single cable known as a backbone cable.
- Each node is either connected to the backbone cable by drop cable or directly connected to the backbone cable.
- The bus topology is mainly used in 802.3 (ethernet) and 802.4 standard networks.
- The configuration of a bus topology is quite simpler compared to other topologies.
- The backbone cable is considered a "single lane" through which the message is broadcast to all the stations.
- The most common access method of the bus topologies is CSMA (Carrier Sense Multiple Access).
- Mesh
- Mesh technology is an arrangement of the network in which computers are interconnected with each other through various redundant connections.
- There are multiple paths from one computer to another computer.
- It does not contain the switch, hub, or any central computer which acts as a central point of communication.
- The Internet is an example of mesh topology.
- Mesh topology is mainly used for WAN implementations where communication failures are a critical concern.
- Mesh topology is mainly used for wireless networks
The correct option is (3)
Concept:-
Median:- Median is also computed for a single attribute /variable at a time. When all the values are sorted in ascending or descending order, the middle value is called the Median.
 Key Points
Key Points
- Median represents the central value at which the given data is equally divided into two parts.
- For an odd number of values, the median is the middle value. For an even number of values, the median is the average of the two middle values.
- Two define the median in one sentence we can say that the median gives us the midpoint of the data.
- Sorting is the process of arranging data in ascending or descending order on the basis of one more column.
 Additional InformationMean:- Mean is simply the average of numeric values of an attribute. Mean is also called average. The mean is a very common measure of central tendency. The mean defines the center of gravity(mass) of the data, it uses all the data, and no sorting is required.
Additional InformationMean:- Mean is simply the average of numeric values of an attribute. Mean is also called average. The mean is a very common measure of central tendency. The mean defines the center of gravity(mass) of the data, it uses all the data, and no sorting is required.
Mode:- The value that appears the most number of times in the given data of an attribute/variable is called mode. It is computed on the basis of the frequency of occurrence of distinct values in the given data.
Range:- It is the difference between maximum and minimum values of data. The range can be calculated only for numerical data. It is a measure of dispersion and tells about the coverage/spread of data values.
The correct option is TRUNCATE
CONCEPT:
TRUNCATE command removes all rows from a table, but the table structure or definition remain.
DROP command can be used to remove the table definition in addition to its data.
DELETE command can be used to remove the specified rows(one or more) of the table.
Syntax:
TRUNCATE TABLE table_name;
DROP TABLE table_name;
DELETE FROM table_name WHERE condition;
The correct answer is option 3.
 Key Points
Key Points
- A firewall is a security device that monitors and controls incoming and outgoing network traffic based on predetermined security rules.
- It acts as a barrier between an untrusted network (like the internet) and a trusted network (like a company's internal network) to prevent unauthorized access to the trusted network.
- Firewalls can be either hardware or software-based and are an essential component of network security.
 Additional Information
Additional Information
- Hub: It is a network device that connects multiple devices in a network, but it does not provide any security features.
- Router: It is a network device that directs traffic between networks, but it has limited security features compared to a firewall.
- Bridge: It is a network device that connects two network segments, but it also does not provide any security features.
A stack can be implemented using two queues. Let stack to be implemented be ‘x’ and queues used to implement be ‘a’ and ‘b’.
Method 1 (By push operation)
This method makes sure that the newly entered element is always at the front of ‘a’, so that pop operation just dequeues from ‘a’. ‘b’ is used to put every new element at front of ‘b’.
Method 2 (By making pop operation costly)
In a push operation, the new element is always enqueued to a. In pop() operation, if b is empty then all the elements except the last, are moved to b. Finally, the last element is dequeued from a and returned.
Therefore Option 2 is correct
The Correct answer is Mesh.
 Key Points
Key Points
- A mesh topology is characterized by multiple connections, offering the highest level of fault tolerance among all network topologies.
- In a mesh topology, every component of the network is directly connected to every other component.
Key characteristics of a mesh topology include:
- Redundant links: A mesh network provides redundant links across the network, ensuring that if one link or component fails, traffic can still be rerouted through alternative paths.
- Rerouting capability: In the event of a break in a segment of cable, data can still be rerouted using other available cables within the network.
- Cost and complexity: Despite its fault tolerance benefits, mesh topologies are rarely used due to the significant cost and effort involved in establishing direct connections between every network component.
- Partial mesh deployments: To balance the need for redundancy with cost considerations, partial mesh topologies are often deployed. These configurations offer a compromise between fault tolerance and resource investment.
 Additional Information
Additional Information
- Bus topology:
- Linear bus topology is a type of network topology where each device connects one after the other in a sequential chain
- The bus topology is designed in such a way that all the stations are connected through a single cable known as a backbone cable.
- Each node is either connected to the backbone cable by drop cable or directly connected to the backbone cable.
- The bus topology is mainly used in 802.3 (ethernet) and 802.4 standard networks.
- The configuration of a bus topology is quite simpler compared to other topologies.
- The backbone cable is considered a "single lane" through which the message is broadcast to all the stations.
- The most common access method of the bus topologies is CSMA (Carrier Sense Multiple Access).
- Star Topology:
- A star topology is designed with each node (file server, workstations, and peripherals) connected directly to a central network hub, switch, or concentrator.
- Data on a star network passes through the hub, switch, or concentrator before continuing to its destination.
- The hub, switch, or concentrator manages and controls all functions of the network.
- It also acts as a repeater for the data flow.
- This configuration is common with twisted pair cable; however, it can also be used with coaxial cable or fiber optic cable.
- Ring Topology;
- In ring topology each node connects to exactly two other nodes, forming a single continuous pathway for signals through each node - a ring.
- Data travels from node to node, with each node along the way handling every packet.
- Because a ring topology provides only one pathway between any two nodes, ring networks may be disrupted by the failure of a single link.
- A node failure or cable break might isolate every node attached to the ring.
The correct answer is Hashing.
This question can be solved by some basic understanding of every type of search.
Let's go one by one -
Binary searching:- In binary searching, you have a sorted array, and you divide that array according to the mid element, Then either you have to go left or right and search till the end until you find the required element.
This involves unnecessary comparison. So, option 1 got eliminated.
Sequential searching:- Here, This searching technique involves Finding a particular value in a list that consists of Checking All of its elements, one at a time and in sequence until the desired element is found.
This involves unnecessary comparison, so, option 2 got eliminated.
Hashing-It is the best searching technique available with O(1) time complexity, it has a table consisting of key-value pairs, and directly with the help of key u can reach to value.
So, no unnecessary comparison is needed,
Refer to the below diagram to understand it better

So, option 3 will be the answer here
Which of the following is/are the built-in exception?
1.TypeError
2.IndentationError
3.ValueError
4.IndexRangeError
TypeError- Raised when a function or operation is applied to an object of the incorrect type.
- For example - using +(addition operator) on a string and an integer value will raise a type error.
IndentationError- Raised when there is an incorrect indentation. Suppose u forget to use indentation in for loop, then the loop will not run at all.
ValueError- Raised when a function gets an argument of correct type but of improper value.
- For example - when a user gives an invalid value to a function.
IndexRangeError- When users try to access an item using a value that is out of index range or does not exist at all. This is not a type of Builtinexception.
So, option 3 will be the answer.
The correct answer is DROP TABLE table_name;.
 Key Points
Key Points
- The DROP TABLE statement is used to remove a table definition and all its data, indexes, triggers, constraints, and permission specifications for that table.
- The correct syntax for dropping a table is DROP TABLE table_name; where table_name is the name of the table you want to drop.
 Additional Information
Additional Information
- Option 1: DROP TABLE table_name is incorrect because it is missing the semicolon (;) at the end, which is required to terminate the SQL statement.
- Option 3: DROP DATABASE table_name; is incorrect because this syntax is used to drop a database, not a table.
- Option 4: DROP TABLE table_name: is incorrect because it uses a colon (:) instead of a semicolon (;), which is not the correct syntax for terminating the SQL statement.
The correct answer is A - B + C $ D + E – F
Explanation:
To convert the postfix expression A B - C + D E F - + $ to its corresponding infix expression, let's follow the postfix to infix conversion process step by step:
Postfix Expression: A B - C + D E F - + $
1. Reading Postfix Expression:
- Operands and operators are read from left to right.
- Use a stack to keep track of operands.
2. Steps:
- Push A to the stack.
- Push B to the stack.
- Read -, pop B and A, form the infix expression (A - B), and push it back to the stack.
- Push C to the stack.
- Read +, pop C and (A - B), form the infix expression (A - B) + C, and push it back to the stack.
- Push D to the stack.
- Push E to the stack.
- Push F to the stack.
- Read -, pop E and F, form the infix expression (E - F), and push it back to the stack.
- Read +, pop D and (E - F), form the infix expression D + (E - F), and push it back to the stack.
- Read $, pop D + (E - F) and (A - B) + C, form the infix expression ((A - B) + C) $ (D + (E - F)).

Infix Expression
- This results in the infix expression: A - B + C $ D + E – F
Comparing with the given options, the correct answer is: A - B + C $ D + E – F
Consider the following relation.
Student(Rno, name, Branch, Year)
| Rno | name | Branch | Year |
| 1 | Balaji | CSE | 1 |
| 2 | Ravi | CSE | 2 |
| 3 | Vijay | CSE | 2 |
| 4 | Sam | IT | 2 |
| 5 | Suman | IT | 2 |
| 6 | Ritu | ME | 1 |
What is the output for the given query?
Query:
Select distinct branch
from student ;
The correct answer is option 1.
Concept:
Distinct Clause:
By default, SQL shows all the data retrieved through query as output. However, there can be duplicate values. The SELECT statement when combined with the DISTINCT clause returns records without repetition (distinct records).
The given data,
Student(Rno, name, Branch, Year)
| Rno | name | Branch | Year |
| 1 | Balaji | CSE | 1 |
| 2 | Ravi | CSE | 2 |
| 3 | Vijay | CSE | 2 |
| 4 | Sam | IT | 2 |
| 5 | Suman | IT | 2 |
| 6 | Ritu | ME | 1 |
Query:
Select distinct branch
from student ;
Step 1:
It selects all the rows in the student table.
Step 2:
DISTINCT clause returns records without repetition Which means distinct records in the attribute branch so it prints only CSE, IT, and ME as output.
Hence the correct answer is option 1.
The correct answer is option 4.
Concept:
Arithmetic Error:
An arithmetic Error is simply an error that occurs during numeric calculations. ArithmeticError types in Python include:
- Over Flow Error.
- Zero Division Error.
- Floating Point Error.
All of these errors have the potential to cause Python programming to crash. Because we do not want our code to fail as a result of improper input from us or a user, it is crucial to capture errors.
Example:
Zero Division Error.:
try:
arithmetic = 5/0
print(arithmetic)
except ArithmeticError:
print('Has error')
Over Flow Error:
import math
try:
print("The exponential value is")
print(math.exp(1000))
except OverflowError as oe:
print("After overflow", oe)
Floating Point Error:
It happens frequently when a system handles floating-point numbers internally. This issue arises from floating-point numbers' underlying representation, which employs a set number of binary digits to represent a decimal integer. Since it might be challenging to convert a decimal integer to binary, roundoff mistakes frequently occur.
Hence the correct answer is All the above.
What will be calculated for the following SQL function?
MOD(X, Y)
The correct option is (1)
Returns the remainder after dividing number X by number Y.
Concept:-
MOD(X, Y): Returns the remainder after dividing number x by number y
Example: MySQL > SELECT MOD(21, 2);
OUTPUT: 1
 Key Points
Key Points
- Three commonly used numeric functions are POWER(), ROUND() and MOD().
- POWER (X, Y) can also be written as POW(X, Y). Its calculates X to the power Y.
- ROUND (N, D), Rounds off number N to D number of decimal places. If D = 0, then it rounds off the number to the nearest integer.
 Key Points
Key Points
- White hats are hackers who use their skills for ethical purposes and to improve security.
- They often work as cybersecurity professionals, identifying vulnerabilities in systems and helping organizations to fix them.
- Unlike black hats, who exploit vulnerabilities for malicious purposes, white hats aim to protect and secure systems.
- White hats often participate in bug bounty programs, where they are rewarded for finding and reporting security flaws.
 Additional Information
Additional Information
- Black hats are hackers with malicious intent, seeking to exploit systems for personal gain or to cause harm.
- Gray hats fall somewhere in between, sometimes violating laws or ethical standards but without malicious intent.
- Cybersecurity is a critical field, and ethical hackers play a vital role in safeguarding information and infrastructure.
- Organizations often conduct penetration testing to assess their security, employing white hats to simulate attacks and identify weaknesses.
Consider the following student relation.
Student relation has Rno, Name, Branch, and year attributes.
| Rno | Name | Branch | Year |
| 101 | A | CSE | 1 |
| 102 | B | CSE | 2 |
| 103 | C | CSE | 2 |
| 104 | D | IT | 2 |
| 105 | E | IT | 2 |
| 106 | F | ME | 1 |
How many names are printed for the given query?
Query:
Select Name
From Student
Where Branch= 'CSE';
The correct answer is option 3.
Concept:
WHERE Clause:
The WHERE clause is used to retrieve data that meet some specified conditions.
Explanation:
The given data,
Student relation has Rno, Name, Branch, and year attributes.
| Rno | Name | Branch | Year |
| 101 | A | CSE | 1 |
| 102 | B | CSE | 2 |
| 103 | C | CSE | 2 |
| 104 | D | IT | 2 |
| 105 | E | IT | 2 |
| 106 | F | ME | 1 |
The given query,
Select name
From student
Where branch= 'CSE';
Here the query first selects the student relation with all rows and columns. After the Where clause is used to retrieve data that meet some specified conditions. The given condition is branch= 'CSE' Hence it prints the three names of student CSE.
Name
A
B
C
Hence the correct answer is 3.
Match the following
| List I (Terms) | List II (Use in) | ||
| A. | ISDN | 1. | Web page |
| B. | URL | 2. | Video-conferencing |
| C. | Firewall | 3. | Internet standard for information transmission |
| D. | HTTP | 4. | Protecting unauthorised access to internet |
 Key Points
Key Points
- ISDN stands for Integrated Services Digital Network and is used for video-conferencing and other digital transmission services.
- URL stands for Uniform Resource Locator, and it is used to specify addresses on the World Wide Web.
- A Firewall is a network security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules, thereby protecting unauthorised access to the internet.
- HTTP stands for Hypertext Transfer Protocol, which is an internet standard for information transmission and is used for transferring web pages.
 Additional Information
Additional Information
- ISDN
- ISDN is a set of communication standards for simultaneous digital transmission of voice, video, data, and other network services over the traditional circuits of the public switched telephone network.
- It provides better quality and higher speeds compared to traditional telephone services.
- URL
- A URL is essentially the address of a resource on the internet.
- It indicates the location of a web page or file and the protocol used to access it.
- Firewall
- A Firewall can be software-based or hardware-based and is critical in protecting networks from cyber threats.
- It works by establishing a barrier between a trusted internal network and untrusted external networks.
- HTTP
- HTTP is the foundation of any data exchange on the Web and it is a protocol used for transmitting hypertext requests and information between servers and browsers.
- It is a stateless protocol, meaning each request from a client to a server is treated as an independent transaction.
The Correct answer is Guided media.
 Key Points
Key Points
- Guided media:
- Guided media refers to the transmission of data through physical paths, such as cables.
- Various types of cables, including coaxial cables, twisted pair copper wires, and optical fiber cables, are used based on factors like network topology, protocol, and size.
- Coaxial cables resemble those used for transmitting cable TV signals, while twisted pair copper wires are similar to phone cables, available in shielded and unshielded varieties.
- Optical fiber cables are also utilized for their high-speed data transmission capabilities.
 Additional Information
Additional Information
- Unguided media:
- Unguided media does not involve the installation of wires.
- Instead, data communication is primarily facilitated through radio waves and microwaves.
- This form of transmission is wireless and enables data transfer over long distances without the need for physical connections.
- Transmission Medium:
- A transmission medium, also known as a communication channel, is the physical pathway used to transmit data signals from one point to another.
- It can be a physical or virtual path, guiding the transmission of data between devices.
- The choice of a transmission medium is determined by various factors including the network's topology, the communication protocol being used, the size of the network, and environmental considerations.
- Different transmission media have their own advantages and limitations, influencing the overall performance and capabilities of the network.
- Modulation:
- Modulation refers to the process of varying a carrier signal's properties, typically a high-frequency wave, to encode information for transmission.
- This encoding allows the transfer of information through a communication channel, such as a wired or wireless medium, without interference or overlapping with other signals in the same medium.
The correct answer is Post Office Protocol.
 Key PointsPost Office Protocol.
Key PointsPost Office Protocol.
- POP is a distinct point where many devices share a connection and communicate with each other.
- It includes high-speed telecommunication devices and technologies.
- A POP has servers, routers, switches, and other network interface equipment that is located in a data center.
- The motive of POP is to provide an easy way for a client computer to retrieve e-mail on an SMTP (Simple Mail Transfer Protocol) server.
- The first version of post office protocol was first introduced in 1984 by the Internet Engineering Task Force.
- Version 2 of POP was published in 1985.
 Additional InformationCharacteristics of POP :
Additional InformationCharacteristics of POP :
- Post Office Protocol is an open protocol.
- It allows access to new mail from a spread of client platform types.
- It supports download and deletes functions even when offline.
- It requires no mail gateways due to its native nature.
- POP can handle email access only when the emails are sent by SMTP.
 Key Points
Key Points
- Encryption is the process of converting plain text into a coded format, known as ciphertext, to prevent unauthorized access.
- It is a crucial aspect of data security, ensuring that sensitive information remains confidential during transmission or storage.
- Encryption algorithms use keys to transform data, and the same or a different key is used to decrypt the information back to its original form.
- Types of encryption include symmetric encryption, where the same key is used for both encryption and decryption, and asymmetric encryption, which uses a pair of keys (public and private).
- Common encryption standards include AES (Advanced Encryption Standard), RSA (Rivest-Shamir-Adleman), and DES (Data Encryption Standard).
 Additional Information
Additional Information
- Decryption is the reverse process of encryption, converting ciphertext back into readable plain text using a key.
- Encryption is widely used in various applications, including online banking, email communications, and securing personal data on devices.
- The strength of encryption depends on the algorithm used and the length of the encryption key; longer keys generally provide stronger security.
The correct answer is option 3.
Concept:
An exception interrupts the flow of the program without interrupting its execution.
Clauses are defined as:
Try: Use to contain the statement of code where an exception can raise.
Except: This clause contains the way to handle a particular exception.
Else: If no exception raises then the else block is used to execute the certain statements. It means else part is executed when no exception occurs. The else block always need to be present after the except block.
Finally: Whether an exception is triggered or not, the finally-block is always performed.
Syntax:
try:
# Some Code...
except:
# optional block Handling of exceptions (if required)
else:
# execute if no exception
finally:
# Some code .....(always executed)
______ consists of a computer network across an entire city, college campus or small region
A computer network is a group of computers linked together for the purpose of communication and sharing resources.

The following are the various types of communication networks:
|
LAN |
WAN |
MAN |
SAN |
|
It stands for Local Area Network. |
It stands for Wide Area Network. |
It stands for Metropolitan Area Network. |
It stands for Storage Area Network. |
|
It is a computer network that spans a relatively small area, usually confined to a single room or within a building or group of buildings. |
It is a network that spans a relatively large geographical area, generally having a radius of more than 1 km. Typically, a WAN consists of two or more LANs. |
A metropolitan area network, or MAN, consists of a computer network across an entire city, college campus or small region. |
SAN (storage area network) is a high-speed network of storage devices that also connects those storage devices with servers. |
|
One LAN can be connected to other LANs over any distance via telephone lines and radio waves. |
Computers connected to a wide-area network are often connected through public networks, such as the telephone system. |
It interconnects users with computer resources in a geographic area or region larger than that covered by even a LAN but smaller than the area covered by WAN. |
It helps attach remote computer storage devices, such as disk arrays, tape libraries, etc. to servers in such a manner that they appear to be locally attached to an OS. |
The correct answer is All are correct.
 Key Points
Key Points
- A cyber attack is a harmful but intentional attempt to breach or cause damage to the software system by an individual or an organization.
- In an Eavesdropping attack, the attacker or hacker intercepts the conversation or modifies the information or thefts the credentials such as passwords or PINs etc.
- This attack is difficult to detect because it is sent over an unsecured client-server connection.
- It is also known as a Phishing or sniffing attack. Hence option 1 is correct.
- This type of attack can be prevented by using a Firewall or Virtual Private Network (VPN). Changing the credentials frequently also helps.

 Additional Information
Additional Information
- In the Denial of Service (DoS) type of attack, the attacker makes the computer or any device inaccessible to the user. The attacker crashes the computer by sending mass data or by increasing the network traffic.
- Man in The Middle (MiTM) is an attack where the attacker intercepts the conversations or reads the entered information in the websites. The attacker usually targets the unsecured network or public Wi-Fi.
- Malware attack is a common type of cyber attack where malicious software executes unauthorized functions. Viruses, Worms, Ransomware, Spyware and Trojans are some of the types.
Which of the following applications may use a stack?
(a) Parenthesis balancing program
(b) Process scheduling operating system
(c) Conversion of infix arithmetic expression to postfix formStack:
- Stack is a data structure which possesses the LIFO property i.e. last in first out. The element which inserted at the last will come out first from the stack.
- Two operations that can be performed on the stack are Push and Pop.
- Push is used to insert element into the stack and pop operation is used to remove element from the top of the stack.
Applications of stack:
1) Expression conversion such as infix to postfix, infix to prefix.
2) Expression evaluation
3) Parsing well-formed parenthesis
4) Decimal to binary conversion
5) Reversing a string
6) Storing function calls
Note:
Queue data structure is used for process scheduling operating system.
The correct option is Divide and Conquer way to search elements
CONCEPT:
Binary search follows the divide and conquer technique.
To search for an element, first, find the middle element, if a match is found, then return the location.
Or, if the element is less than the middle element search will proceed in the left half, else the search will proceed into the right half.
Example:
List = [7, 12, 27, 30, 43] with index range from 0 to 4. and Key to search = 12
| Left index | Right Index | Middle | Middle vs Key | Number of Comparisons | Logic |
| 0 | 4 | (0+4)/2=2 | 27>12 | 1 | Middle is > key then we set right = mid-1 |
| 0 | 1 | (0+1)/2=0 | 12==12 | 2 | As the middle = key then Search is successful. |
Thus the above searching takes 2 iterations for binary search to search key 12.
Aggregate functions return a single result row based on groups of rows, rather than on single rows. Aggregate functions can appear in select lists and in ORDER BY and HAVING clauses.
 Key Points
Key Points
|
Function |
Description |
|
COUNT |
COUNT returns the number of rows returned by the query |
|
AVG |
AVG returns average value of expression |
|
MIN |
MIN returns minimum value of expression |
|
SUM |
SUM returns the sum of values of expression |
In SQL, AVG is an aggregate function
The correct answer is Double-ended queue.
 Key Points
Key Points
- A Double-ended queue (Deque) is a type of data structure that allows insertion and deletion of elements at both the front and the rear ends.
- This flexibility makes Deque a hybrid structure that can act as both a stack and a queue.
- Deques are used in various applications like managing a list of tasks, web browser history, and more.

 Additional Information
Additional Information
- Simple queue: In a simple queue, elements are added at the rear end and removed from the front end. It follows the First-In-First-Out (FIFO) principle.
- Circular queue: A circular queue is a type of queue where the last position is connected back to the first position to make a circle. It efficiently utilizes memory by preventing the "queue full" condition when there are vacant slots at the front.
- Priority queue: In a priority queue, each element is associated with a priority. Elements are served based on their priority rather than their position in the queue.
What will be the results of the following MySQL statement:
SELECT RIGHT('TestBook', 4);
The correct option is (3)
Book
Concept:-
String function:- String functions can perform various operations on alphanumeric data which are stored in a table. They can be used to change the case (uppercase to lowercase or vice versa), extract a substring, calculate the length of a string, and so on.
Explanation:
String function, RIGHT(string, N) returns N number of characters from the right side of the string.
Here given the MYSQL statement,
MySQL > SELECT RIGHT("TestBook", 4);
The trail of the string will be traversed from the right side.
Output: Book
 Key Points
Key Points
- LEFT(string, N), Returns N number of characters from the left side of the string. For example, MySQL>SELECT LEFT ("Computer", 4); the output is Comp.
- LENGTH(string) Return the number of characters in the specified string. For example, MySQL> SELECT LENGTH(" informatics"); the output is 11.
Consider the following student relation.
Student relation has Rno, Name, Branch, and year attributes.
| Rno | Name | Branch | Year |
| 101 | A | CSE | 1 |
| 102 | B | CSE | 2 |
| 103 | C | CSE | 2 |
| 104 | D | IT | 2 |
| 105 | E | IT | 2 |
| 106 | F | ME | 1 |
How many rows of data are printed for the given query?
Query:
Select Branch, year, Count(*)
From student
Group by Branch, year;
The correct answer is option 4.
Concept:
GROUP BY:
The GROUP BY statement groups rows that have the same values into summary rows.
Explanation:
The given data,
Student relation has Rno, Name, Branch, and year attributes.
| Rno | Name | Branch | Year |
| 101 | A | CSE | 1 |
| 102 | B | CSE | 2 |
| 103 | C | CSE | 2 |
| 104 | D | IT | 2 |
| 105 | E | IT | 2 |
| 106 | F | ME | 1 |
The given query,
Select Branch, year, Count(*)
From student
Group by Branch, year;
Here the query first selects the student relation with all rows and columns. After the group by clause divide that table into groups based on the branch and year with select Branch, year, and Count(*) in each group.
Branch year Count
CSE 1 1
CSE 2 2
IT 2 2
ME 1 1
Hence the correct answer is 4.
The correct answer is MS Excel.
 Key Points
Key Points
- MS Excel is not an example of a Relational Database Management System (RDBMS).
- Excel uses spreadsheets, while RDBMS uses tables.
- Excel is suitable for small to medium-sized datasets, while RDBMS can handle large volumes of data.
- Excel allows single-user editing, while RDBMS supports multi-user access.
- Excel lacks a full-fledged query language like SQL, which RDBMS provides.
 Additional Information
Additional Information
- MS SQL Server:
- Developed by Microsoft, it's a robust RDBMS designed for enterprise-level data management.
- Offers advanced features like transaction processing, data warehousing, and business intelligence.
- Provides high availability, scalability, and security features for mission-critical applications.
- IBM DB2:
- Developed by IBM, it's a powerful RDBMS with a long history in the enterprise space.
- Supports various operating systems including Windows, Linux, and UNIX.
- Known for its reliability, scalability, and performance in handling large-scale databases.
- MySQL:
- An open-source RDBMS, widely used for web applications and small to medium-sized databases.
- Offers features such as multi-user access, data security, and transaction support.
- Known for its ease of use, flexibility, and strong community support.
The correct answer is Node that is connected to two or more networks.
 Key Points
Key Points
- A gateway or router is a device that connects two or more networks, allowing them to communicate with each other.
- Routers operate at the network layer (Layer 3) of the OSI model and are responsible for forwarding data packets between networks based on their IP addresses.
- Gateways can operate at various layers of the OSI model and can perform protocol conversions to enable communication between different network architectures or protocols.
- Routers use routing tables and protocols such as OSPF, BGP, and RIP to determine the best path for data packets to reach their destination.
- Gateways are often used to connect different types of networks, such as a local area network (LAN) to a wide area network (WAN) or to the internet.
- Common manufacturers of routers and gateways include Cisco, Juniper Networks, and Netgear.
 Additional Information
Additional Information
- Routers can also provide additional functions such as network address translation (NAT), firewall protection, and quality of service (QoS) management.
- Gateways can be used to connect networks that use different communication protocols, such as Ethernet and Token Ring.
- Modern routers often come with built-in wireless access points to provide Wi-Fi connectivity in addition to wired connections.
- Gateways can also act as proxies or firewalls to control traffic between networks and enhance security.